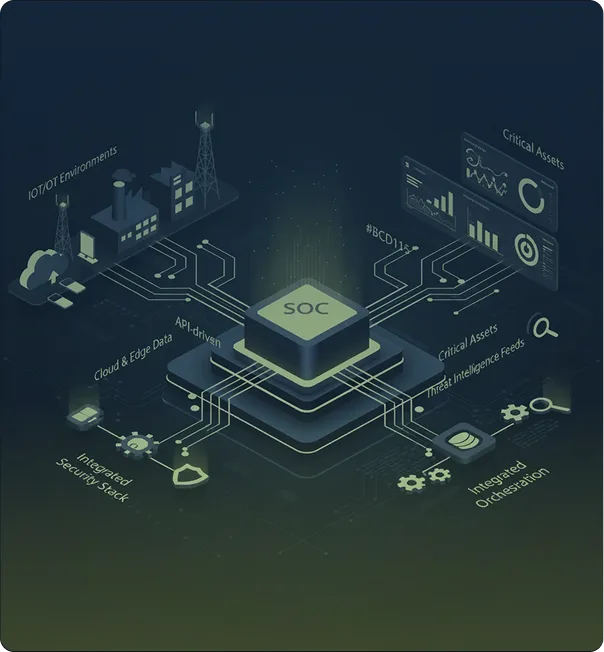
Federated SOC framework combining customer SIEM/SOAR with GSL Virtual SOC
Integration layer ingesting telemetry from on-prem and cloud systems
Common data model to normalize events across diverse tools
Secure, API-driven exchange with customer-managed infrastructure and logging
Optional co-hosted environments or shared-control deployment models
End-to-end visibility across IT, OT, cloud and critical assets